AI Agent On-Premise Security
Protect models, data, and keys processed by LLM-based AI agents with Post-Quantum Cryptography and hardware security chips. Your enterprise AI assets never leave your infrastructure.
In the Age of AI Agents, Hardware Security Is Non-Negotiable
Model Weight Exposure Threats. LLM model weights residing in memory during inference cannot be fully protected by software alone. 85% of enterprises are exposed to this vulnerability, and side-channel attacks and model extraction attacks demand hardware-level security.
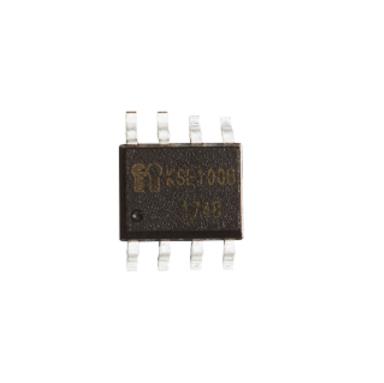
Prompt & Data Leakage Risk. Confidential enterprise documents and prompts can be exfiltrated through cloud AI services. Keypair's KSE security chips and QORA PQC are deployed at critical points in the AI inference pipeline to completely prevent data exfiltration.
Preparing for the Quantum Era. QORA applies NIST PQC standard algorithms — CRYSTALS-Kyber, Dilithium, and Sphincs+ — to provide security that remains safe against quantum computing threats. Combined with on-premise infrastructure, it meets the strict compliance requirements of finance, defence, and healthcare.
QORA PQC-Based 4 Core Security Features
Post-Quantum Cryptography-based AI Agent security solution for the quantum computing era
PQC-Based Model Encryption
LLM model weights are encrypted with NIST PQC standard CRYSTALS-Kyber, and SHA-3-based integrity verification runs before every inference session. Protects model IP from quantum computing threats.
Real-Time Quantum-Resistant Data Encryption
Prompt inputs, context data, and inference outputs are encrypted with PQC algorithms in real time across memory and transit. End-to-end PQC encryption prevents data leakage.
Hybrid Encryption Secure Key Vault
API keys, model decryption keys, and authentication tokens are stored in the KSE chip's secure enclave with PQC + AES-256 dual encryption. Keys are never directly accessible from the software layer.
Physical Tamper Detection & Auto-Response
Physical intrusion attempts are detected in real time, and PQC key material is immediately zeroized upon threat detection. 24/7 monitoring ensures physical security within the data center.
QORA On-Premise AI Security Architecture
AI Agent → QORA PQC → KSE Security → Enterprise Assets — 4-layer security based on post-quantum cryptography
Industry-Specific AI Agent Security Scenarios
Providing tailored security solutions across finance, defence, healthcare, and manufacturing industries
Financial AI Agents
Protects customer financial data processed by credit scoring and fraud detection AI at the hardware level. Meets financial regulatory and data privacy requirements.
Defence & Public Sector AI
Secures models and data for intelligence analysis and operational planning AI with KCMVP-certified security chips. Prevents leakage of classified and government-sensitive data.
Healthcare AI Agents
Encrypts inference data for medical imaging analysis and diagnostic AI to comply with HIPAA, GDPR, and local data protection regulations.
Manufacturing & Industrial AI
Protects production data and trade secrets handled by process optimization and predictive maintenance AI. Guarantees secure inference in air-gapped environments.
Deployment Process
A systematic 4-step deployment process for building a secure and efficient AI Agent security solution
Security Consulting
Internal infrastructure analysis and security requirements definition
PoC Design
Pilot scenario setup and small-scale verification environment
Build & Integration
KSE security chip deployment and existing system integration
Enterprise Rollout
Performance verification, scaling, and ongoing operational support
Inquiries
Need an AI Agent Security Solution?
Consult with our experts and design a tailored security architecture. We'll get back to you within 24 hours.